Introduction
Chemical toll manufacturing rests on a fundamental tension: to scale production, brands must hand over their most valuable competitive assets—precise ingredient ratios, synthesis pathways, temperature and pressure parameters, even raw material supplier identities. Unlike a product design visible on shelves, these formulations exist only in protected documentation.
That creates a precarious position: your IP must be shared to enable production, yet that same sharing opens the door to unauthorized replication.
This risk is especially acute in specialty chemicals. Personal care brands rely on proprietary UV filter dispersions, flavour houses guard signature aroma molecule blends, and advanced polymer formulators protect masterbatch compositions — all depending on formulation secrecy to maintain market position.
A weak confidentiality framework can hand a competitor effectively the same formulation without them funding a single day of R&D — not through espionage, but through routine business practices at an inadequately controlled toll facility.
Protecting against that risk requires more than a standard NDA. This guide covers:
- Who bears the greatest exposure in a toll relationship
- What information qualifies as protectable IP
- How chemical-specific NDAs differ from generic templates
- Operational safeguards that go beyond contracts
- How to vet a toll partner's confidentiality maturity
- Actionable steps if a breach occurs
TLDR
- Chemical toll manufacturing requires sharing formulations, process sequences, and raw material identities—all protectable as trade secrets
- Generic NDAs fall short—chemical contracts need formulation exclusivity, sub-contractor restrictions, data destruction protocols, and explicit non-use clauses
- Process fragmentation, access controls, and periodic audits reduce exposure—even within trusted partner relationships
- Vet partners on confidentiality architecture, not NDA willingness alone—ask about access controls, firewall procedures, and certifications
- Enforcement depends on pre-defined remedies and documented IP ownership—establish both before a breach happens
Why Confidentiality Failures Are Especially Costly in Chemical Toll Manufacturing
What Qualifies as Protectable IP in Chemical Manufacturing
In chemical toll manufacturing, intellectual property extends well beyond a finished product's appearance or packaging. Protectable trade secrets include:
- Formulation composition: exact ingredient identities, concentration ratios, and sequencing order
- Process parameters: temperature ranges, pressure levels, reaction times, mixing speeds, and cooling rates
- Synthesis routes: reaction sequences, catalyst selections, and purification methods
- Raw material specifications: supplier identities, grade requirements, and sourcing specifications
- Performance data: stability test results, application-specific efficacy benchmarks, and scale-up learnings
These details cannot be observed externally. They must be disclosed to the toll manufacturer to enable production—creating the exposure that standard product manufacturing does not face.
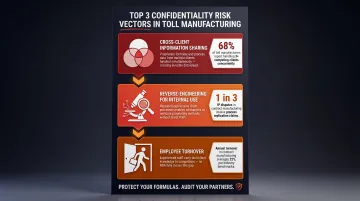
Three Primary Risk Vectors
Confidentiality breaches in toll relationships typically occur through three channels:
Cross-client information sharing: A toll manufacturer serving multiple brands in personal care may inadvertently—or deliberately—apply process insights from one client's UV filter formulation when developing another client's product in the same category.
Reverse-engineering for internal use: Toll partners may analyse client formulations to improve their own product lines or technical capabilities, even without directly disclosing the data to third parties. According to legal analysis by Skadden, toll manufacturers typically already possess expertise in the relevant field, positioning them to compete during or after the agreement.
Employee turnover: When production staff, quality controllers, or R&D personnel leave a toll facility, they carry process knowledge in memory. Approximately 85% of trade secret theft cases involve a current or former employee or trusted business partner.
Compounding Risk in Multi-Partner Models
Asset-light toll manufacturing models, which distribute production across multiple sub-contracted facilities, amplify these risks. When a primary toll partner sub-contracts blending to one facility, encapsulation to another, and quality testing to a third, formulation data travels far beyond the initial contractual relationship—often without explicit disclosure or additional NDA coverage.
Specialty chemicals amplify this problem: different process steps require different equipment, so multi-facility models are the norm rather than the exception. Each handoff multiplies exposure, and few clients maintain visibility into which downstream partners hold their data.
Commercial Consequences Specific to Specialty Chemicals
These exposure risks translate directly into commercial damage. When a breach occurs, the consequences stack quickly:
- Loss of first-mover advantage: A competitor launching a near-identical formulation erases months or years of R&D lead time
- Commoditisation: Proprietary formulations become functionally generic when multiple suppliers can replicate them, compressing margins
- Re-formulation costs: Brands must invest in new R&D to differentiate again, often under time pressure
- Regulatory scrutiny: In personal care or pharmaceutical-adjacent sectors, ingredient disclosure breaches may trigger compliance reviews or labelling audits
- Downstream customer attrition: Brand customers who selected a supplier based on formulation uniqueness may terminate contracts if differentiation disappears
Legal Distinction: Confidentiality Failure vs. Trade Secret Misappropriation
Not all confidentiality lapses constitute legally actionable trade secret theft. Under frameworks such as the US Defend Trade Secrets Act (18 U.S.C. § 1839), information qualifies for protection only if the owner has taken "reasonable measures" to keep it secret and the information derives independent economic value from secrecy.
That legal threshold matters practically. The contractual and operational steps outlined in this guide are not merely best practices—they are prerequisites for legal recourse. A brand that fails to implement access controls, mark documents as confidential, or audit partner compliance may find itself unable to enforce even a well-drafted NDA.
Annual U.S. losses from trade secret theft are estimated at $180 billion to $540 billion, equivalent to 1-3% of GDP. Yet only 1,200 to 1,400 misappropriation cases are filed annually in U.S. courts, suggesting the vast majority of incidents go unprosecuted—often because victims cannot demonstrate they took sufficient protective measures.
What a Strong Chemical Toll Manufacturing NDA Must Include
Why Generic Templates Fail
Standard NDA templates designed for general business use are inadequate in chemical toll contexts. A generic "Confidential Information" clause rarely defines scope with the precision needed to protect formulations, and courts have routinely rejected overly broad or vague definitions in trade secret disputes.
A chemistry-specific NDA must explicitly enumerate protected information types:
- Formulation compositions (ingredient lists, ratios, sequences)
- Synthesis and blending process instructions
- Process parameters (temperatures, pressures, reaction times)
- Batch records and production logs
- Analytical methods and quality control data
- Raw material supplier identities and specifications
- Scale-up data and yield optimization learnings
Sub-Contractor and Affiliate Disclosure Clause
This is the most commonly overlooked—and exploited—gap in toll manufacturing NDAs. The agreement must explicitly state whether the toll partner may share any information with sub-contractors, and if permitted, under what conditions.
Minimum requirements:
- Sub-contractor disclosure is prohibited unless prior written consent is obtained
- Any permitted disclosure requires a back-to-back confidentiality agreement with terms equivalent to or stricter than the primary NDA
- The primary toll partner remains liable for any breach by a sub-contractor
- The client retains the right to approve or reject specific sub-contractors based on their confidentiality posture
Data Handling and Destruction Obligations
The NDA should specify operational data management requirements. These four provisions form the operational backbone of any compliant data handling clause:
- Specifies which systems — cloud, on-premises servers, or physical files — will store confidential information
- Defines who within the toll partner's organization has access and under what authentication requirements
- Sets a retention period for batch records, formulation documents, and process logs
- Requires return or destruction of all confidential copies at contract end, with written certification provided to the client
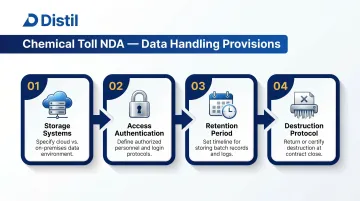
Holland & Knight's NDA analysis emphasises that the absence of destruction protocols is a common failure point, leaving confidential materials accessible long after the business relationship ends.
Non-Compete and Non-Use Clause
Confidentiality alone prohibits disclosure but does not prevent use. A toll partner could comply with a confidentiality obligation while still applying process learnings to serve other clients or develop competing products.
A non-use clause must explicitly prohibit:
- Using the client's formulation or process knowledge to benefit other clients
- Developing internal products based on the client's IP
- Applying insights from the client's scale-up process to unrelated projects
- Sharing "residual knowledge" (information retained in unaided memory) in any commercial context
According to Holland & Knight, a non-use clause may provide broader protection than trade secret law alone — covering information that doesn't qualify as a statutory trade secret but still confers competitive advantage.
Survival and Post-Termination Obligations
The NDA must specify how long obligations continue after the agreement ends:
- Trade secrets: Confidentiality obligations should survive indefinitely, as long as the information retains trade secret status
- Confidential business information: For data that may not meet statutory trade secret thresholds, survival periods typically range from 3–5 years post-termination in specialty chemicals
Survival periods address duration, but the mechanics of wind-down matter equally. Post-termination clauses should also require:
- Return or certified destruction of all physical samples, lab notebooks, and reference standards
- Deletion of all digital copies, including backups, with written confirmation
- Continuing prohibition on hiring employees who had access to the client's formulation for a defined period
Operational Best Practices: Protecting Your IP Beyond the NDA
Process Fragmentation as a Structural Control
Rather than sharing a complete formulation with a single toll manufacturer, structured disclosure involves providing only the information necessary for each partner to perform their specific step.
Example architecture:
- A blending partner receives ingredient identities and ratios but not the synthesis route or raw material supplier identities
- A quality control partner receives performance specifications and test methods but not formulation composition
- A packaging partner receives handling requirements but no formulation data
Academic research by Gooris & Peeters, analyzing 581 foreign service implementations across 19 home countries and 59 host countries, confirms that firms respond to weak IP protection by fragmenting operations, ensuring no single production unit holds complete architectural knowledge.
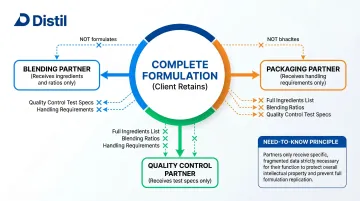
Distil's asset-light model structures this as a control layer: clients retain full data ownership, and access is granted on a permission basis. No single partner within the 20+ facility network holds the complete formulation picture.
Need-to-Know Access Controls at the Toll Facility
Beyond fragmenting across partners, clients should negotiate access restrictions within each facility:
- Limit formulation access to named individuals, not departments
- Require written consent before substituting named personnel
- Exclude seasonal and contract workers from formulation-sensitive operations
- Restrict formulation documents from shared network drives
- Implement password protection and encryption for all digital formulation files
- Require access logs showing who viewed formulation data and when
Skadden's toll manufacturing guidance recommends requiring the toll partner to provide copies of employment contracts for all employees with formulation access, ensuring those contracts include confidentiality obligations, non-compete provisions, and IP assignment clauses.
Periodic Confidentiality Audits
Signing an NDA at contract inception is insufficient. Clients should build the right to audit the toll partner's information security practices into the original agreement, with audits conducted:
- Annually, as a baseline
- Upon any change in facility ownership or management
- After any cybersecurity incident or employee departure involving formulation-exposed personnel
- Before renewing or extending the manufacturing agreement
Each audit should cover the full information security picture, not just access records.
Audit scope should include:
- Review of data access logs
- Verification that all employees with formulation access have signed current confidentiality agreements
- Confirmation that no sub-contractors have been engaged without written client approval
- Inspection of physical and digital storage security
- Assessment of document destruction procedures for terminated projects
Staged Disclosure as a Due Diligence Tool
Before sharing full formulation details, structure the relationship to begin with partial technical disclosure under NDA. Share basic process requirements and observe how the partner handles that information before progressing to complete formulation sharing.
Staged approach:
- Sign a mutual NDA covering general discussions before any technical exchange
- Share process capability requirements only — withhold formulation at this stage
- Evaluate the partner's documentation practices, communication discipline, and responsiveness to confidentiality queries during an observation period
- Disclose formulation incrementally, conditioning each phase on satisfactory handling of the previous one

If a partner mishandles information at stage two, you've protected the formulation entirely — and have a clean basis to exit the relationship before material IP is at risk.
How to Evaluate a Toll Partner's Confidentiality Practices
Signal-Reading Questions for Due Diligence
A partner who has built confidentiality into their operational culture will answer these questions readily and specifically:
NDA timing: Do they offer mutual NDAs early in discussions, or only sign when pushed? A partner who treats confidentiality as standard procedure won't wait to be asked.
Named access: Can they identify by name which specific employees will access your formulation? Vague answers ("our production team") signal inadequate access controls.
Segregated data systems: Do they maintain auditable, client-specific data environments, or store all formulations in shared drives?
Competitive firewall mechanisms: Have they served clients in your product category before? If so, how do they structurally prevent cross-contamination of IP? Ask for specific examples, not assurances.
Sub-contractor disclosure: Do they proactively disclose sub-contractor relationships, or do you have to ask? What is their standard process for obtaining client approval before engaging sub-contractors?
These questions reveal whether confidentiality is embedded in a partner's operating model or treated as a compliance checkbox. Distil's single-point-of-contact model addresses this directly: one accountable manager coordinates the full production journey, limiting formulation exposure to a small, identifiable group rather than a broad production team.
Third-Party Certifications as Confidentiality Proxies
No certification directly validates confidentiality practices, but several quality and information security standards signal disciplined data handling:
ISO 9001:2015: Requires documented information security and access control procedures. Clause 7.5.3 mandates that documents be reviewed and approved before issuance, that access controls include password-protected files and encryption, and that disposal procedures include shredding and secure electronic deletion.
ISO/IEC 27001:2022: Certification in information security management systems demonstrates commitment to protecting data confidentiality, integrity, and availability.
GMP (Good Manufacturing Practice): While focused on product quality and safety, GMP systems require process documentation, batch record integrity, and controlled access—practices that support confidentiality.
ChemStewards: A management system program covering environmental, health, safety, and security performance in chemical manufacturing. Security is one of its core pillars, with a three-year audit cycle.
Ask prospective partners which facilities in their network hold these certifications, and request copies of recent audit reports.
Evaluating Track Record on Confidentiality
Request client references specifically from companies in adjacent (not identical) product categories. Ask references directly:
- How disciplined is the partner in limiting access to formulation data?
- Have you observed any confidentiality lapses, even minor ones?
- How transparent is the partner about sub-contractor use?
- How responsive are they to confidentiality audit requests?
- Has the partner proactively flagged potential conflicts of interest with other clients?
Red flags in track record:
- Frequent personnel turnover in production or quality roles (increases inadvertent disclosure risk)
- History of engaging sub-contractors without prior client notification
- Ownership changes within the past 18 months (may have altered confidentiality culture)
- Reluctance to provide references from direct competitors in adjacent categories
Breach Scenarios and Remedies: What to Do When Things Go Wrong
Early Warning Signs
Confidentiality breaches in toll manufacturing rarely announce themselves. Watch for these indicators:
- A competitor launches a product with suspiciously similar performance characteristics or ingredient positioning shortly after your production begins
- Your raw material supplier receives an inquiry from an unknown buyer with identical grade specifications and sourcing requirements
- A former employee of the toll facility joins a competitor and that competitor's product roadmap shifts toward your formulation category
- The toll partner begins offering "similar" formulations to other clients as standard products
When any of these signals appear, document immediately. Gather evidence of your original IP ownership, the timeline of disclosure to the toll partner, and the nature of the suspicious activity. This documentation is critical before any formal action.
Contractual Remedies
Well-drafted toll manufacturing agreements include specific breach remedies:
Injunctive relief: Immediate court orders to stop further disclosure or use of the formulation. Under the Defend Trade Secrets Act (18 U.S.C. § 1836), U.S. courts may issue injunctions to prevent actual or threatened misappropriation.
Monetary damages: Compensation for actual loss, unjust enrichment gained by the toll partner, or a reasonable royalty. The DTSA permits exemplary damages up to 2x the award for wilful and malicious misappropriation, plus attorney's fees.
Liquidated damages: Pre-defined financial penalties for breach, specified in the agreement. These avoid the need to prove actual damages and accelerate resolution.
Termination clauses: The right to immediately terminate the manufacturing relationship upon breach, with return or destruction of all confidential materials.
Legal Protections
India: No standalone trade secrets statute exists, but protection is available through multiple legal instruments: common law breach of confidence, the Indian Contract Act 1872, and the Information Technology Act 2000. Civil remedies include injunctions, damages, and return of proprietary information. The 22nd Law Commission has recommended the Protection of Trade Secrets Bill 2024, which would codify definitions and remedies — a significant development for manufacturers operating through Indian toll partners.
United States: The Defend Trade Secrets Act provides federal civil remedies, including ex parte seizure orders in extraordinary circumstances. The trade secret definition under 18 U.S.C. § 1839 is broad, covering formulas, patterns, compilations, methods, techniques, and processes, as long as the owner took reasonable measures to maintain secrecy.
Practical Steps Upon Confirmed Breach
- Secure all documentation: Gather the original NDA, formulation disclosure records, batch records, communications referencing confidentiality obligations, and evidence of the breach
- Notify legal counsel: Engage IP litigation specialists with experience in trade secret misappropriation in your jurisdiction
- Formally notify the toll partner: Send written notice of the alleged breach, referencing specific contractual obligations violated
- Preserve evidence: Request that the toll partner preserve all records, communications, and materials related to your formulation (this is a legal hold request)
- Assess damage scope: Determine how widely the information has been disclosed and which downstream parties may have received it
- Invoke contractual remedies: Exercise termination rights, demand return or destruction of materials, and pursue liquidated damages if specified
- Evaluate litigation: Based on evidence strength, jurisdictional advantages, and cost-benefit analysis, decide whether to pursue trade secret misappropriation claims
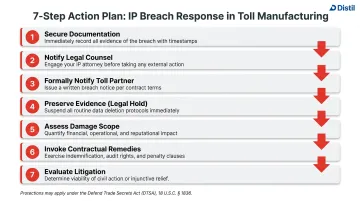
The strength of your position depends almost entirely on the quality of the original NDA and the "reasonable measures" you took operationally. Courts are reluctant to enforce protection for information the owner treated casually.
Frequently Asked Questions
What is a toll manufacturing company?
A toll manufacturing company processes raw materials supplied by the client into finished or semi-finished goods, charging a fee (the "toll") for use of its facilities, equipment, and labour. The client retains ownership of materials and formulations throughout.
What are toll manufacturing costs?
Toll manufacturing costs typically include a processing fee based on batch volume, production complexity, and equipment requirements, plus ancillary costs for quality testing, packaging, and storage. The client covers raw material costs separately.
What should a chemical toll manufacturing NDA include?
A chemistry-specific NDA needs to cover several specific areas beyond a standard agreement:
- Defines confidential information to include formulations, process parameters, batch records, and supplier identities
- Restricts sub-contractor disclosure explicitly
- Specifies post-termination data destruction obligations
- Contains a non-use clause separate from the confidentiality obligation
Can a toll manufacturer legally use your formulation for other clients?
Without a specific non-use clause, a toll manufacturer is bound only by confidentiality. That means they cannot disclose the formulation but may argue they can apply process learnings more broadly. A non-use clause explicitly prohibits any application of the client's IP outside the contracted scope.
How do you protect your formulation when using a toll manufacturer with multiple clients?
The most effective safeguard is process fragmentation—disclosing only the information necessary for each production step—combined with named-individual access controls at the facility and a contractual right to audit the partner's data handling practices.
What are the biggest confidentiality risks in chemical toll manufacturing?
Three risks account for most confidentiality failures in toll manufacturing:
- The toll partner shares formulation data with sub-contractors not bound by NDA
- The toll partner reverse-engineers process parameters for their own product line
- Inadvertent disclosure occurs through employee turnover at the toll facility